-
01
 Topwalk-IBMS
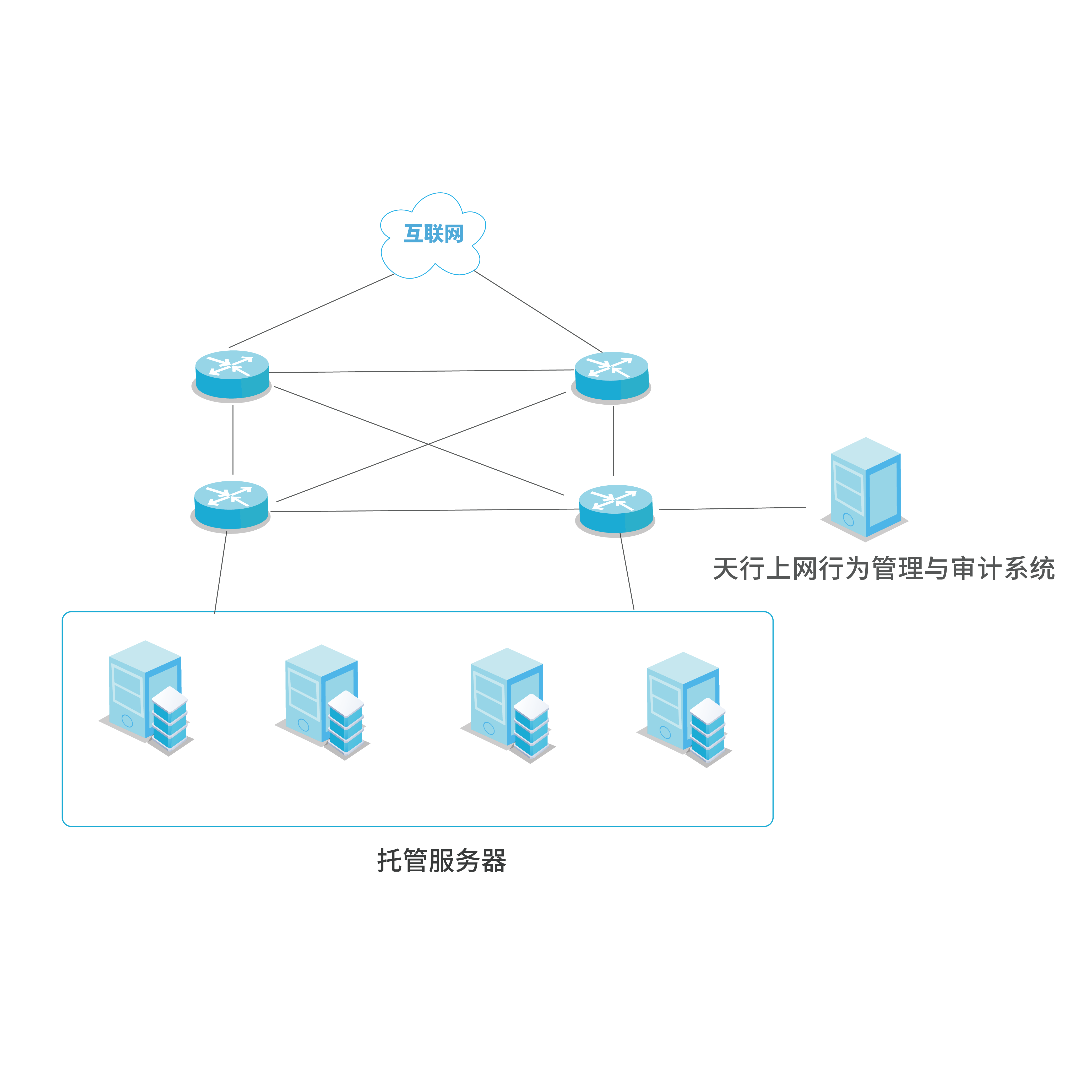
Topwalk-IBMSDeployment modes can be flexibly selected as bypass or routing based on actual user requirements. Routing mode is typically deployed at public network egresses or Layer 3 switch nodes; it provides NAT and other egress networking capabilities while implementing traffic control, behavior auditing, and management for internal network users. Bypass mode preserves the customer’s existing network architecture by mirroring target traffic to the device via the switch’s mirror port, enabling seamless user behavior analysis and auditing. The system conducts in-depth data parsing and reconstruction, analyzes the 7-layer traffic model of bearer services, and retains complete logs including internet access behavior records and application traffic data.